Test all components of your IT infrastructure
Networks
We will identify potential security weaknesses in your network with the help of both internal and external testing scenarios. We check all aspects of network security, such as:
- Wireless network and VPN vulnerabilities
- Firewall and IDS/IPS evasion
- DNS vulnerabilities
- Email and file server vulnerabilities
- Database vulnerabilities
- DHCP vulnerabilities
- Directory services vulnerabilities
Web applications
Our experts will find vulnerabilities within your web applications utilizing manual inspection and dedicated tooling to catch the interactions between client and server. Various aspects are checked as part of our web application pentesting, namely:
- Identity management
- Authentication and authorization
- Session management
- Client-side testing
- APIs
- Cryptography
Mobile applications
Soin Media will perform meticulous manual and automated scans to make sure that your mobile applications can withstand any malicious attack. We can perform a wide range of tests, including:
- Application architecture analysis and reverse engineering
- Authentication and authorization
- Data storage, transition security, and integrity checks
- Encryption algorithms and cryptographic protocols
- Server-side APIs and client-side storage analysis
- Cross-origin resource sharing (CORS) configuration
Social engineering
We will help you tailor and refine policies and security training programs that enhance your protection against cybersecurity threats caused by the human factor. Test your employees with various scenarios:
- Awareness and phishing email simulations
- USB drop tests
- Physical security and tailgating
- Pretexting
- Social media practice reviews
What can a penetration testing company do for your business?
Prevent revenue losses
Save money by preventing costly security breaches and their associated expenses, including legal fees and fines.
Maintain a solid brand reputation
Enhance trust with your customers, partners, and stakeholders by preventing the risks of data breaches.
Avoid service interruptions
Maintain a solid defense against cyber attacks, allowing your business to operate normally without service interruptions at all times.
Meet regulatory requirements
Ensure compliance with data protection laws and industry standards that mandate regular security assessments.
Improve existing mitigation strategies
Continuously improve your security posture, staying ahead of emerging threats, and evolving cyber attack techniques.
Actionable Remediation roadmaps
Instead of just handing you a list of problems, we provides you a detailed, prioritized roadmap.
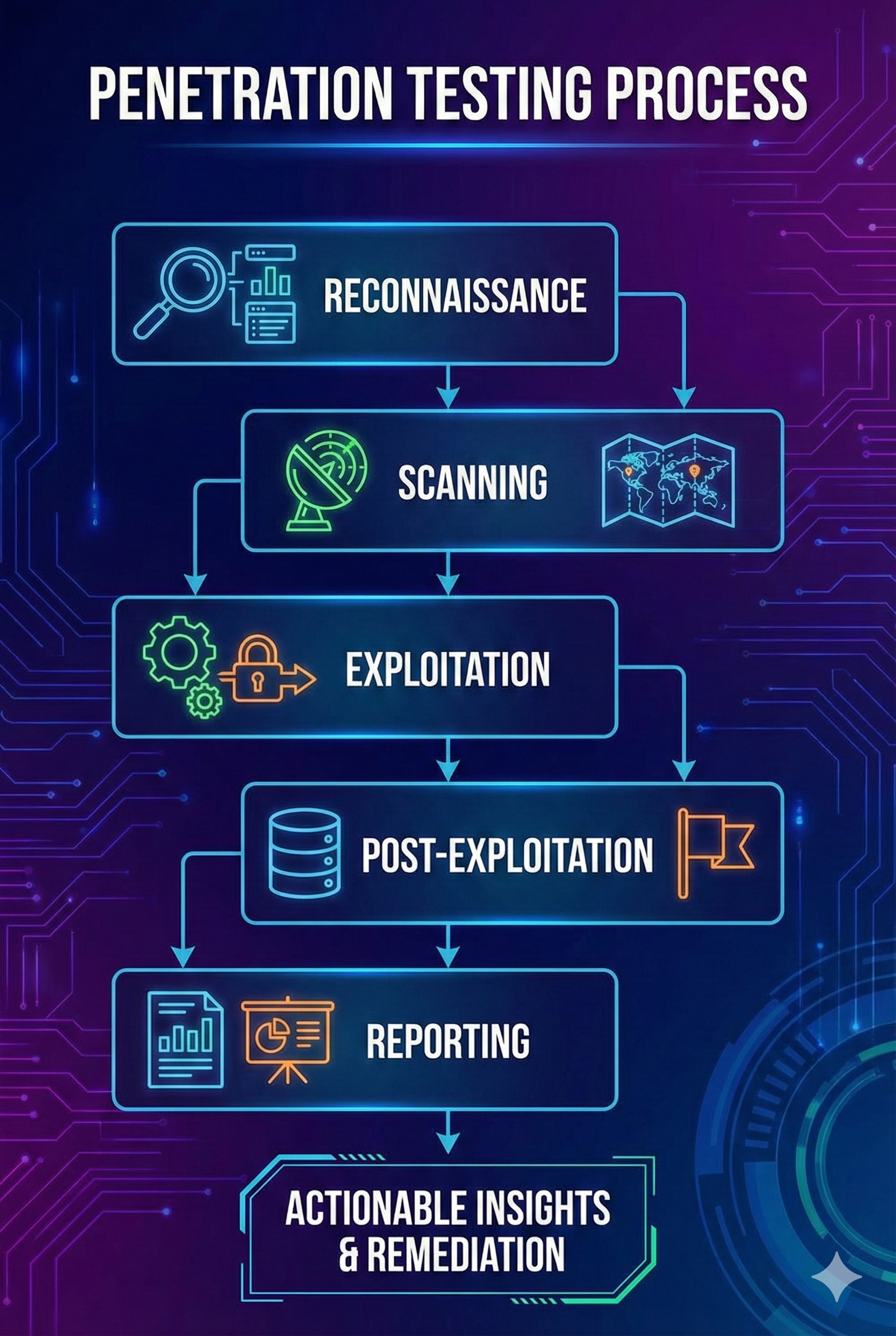
Our approach to penetration testing consulting